Healthcare cyber risk is evolving beyond isolated breaches and becoming a systemic challenge. In this episode...
Podcasts
Explore our latest podcast, Exploited: The Cyber Truth, where we expose real-world cyber threats and the strategies used to stop them—featuring bold conversations with top experts protecting critical infrastructure. You can also revisit episodes of our original series, Lessons from the School of Security Hard Knocks, where leaders reflect on hard-earned lessons from the frontlines of cybersecurity.
Trust at Machine Speed: AI, DevSecOps, and Zero Trust in National Security Software
In this episode of Exploited: The Cyber Truth, Paul Ducklin speaks with Nicolas Chaillan, host of In the Nic of...
The Invisible Attack Surface: Cybersecurity for Embedded Systems
In this episode of Exploited: The Cyber Truth, Paul Ducklin sits down with RunSafe Security CEO Joseph M. Saunders...
AI vs. Vulnerabilities: Who Really Wins?
Artificial intelligence is rapidly changing cybersecurity, but not necessarily in the way headlines suggest. In...
AI Wrote the Code—Who Owns the Risk?
In the Season 2 premiere of Exploited: The Cyber Truth, host Paul Ducklin is joined by RunSafe Security CEO Joseph...
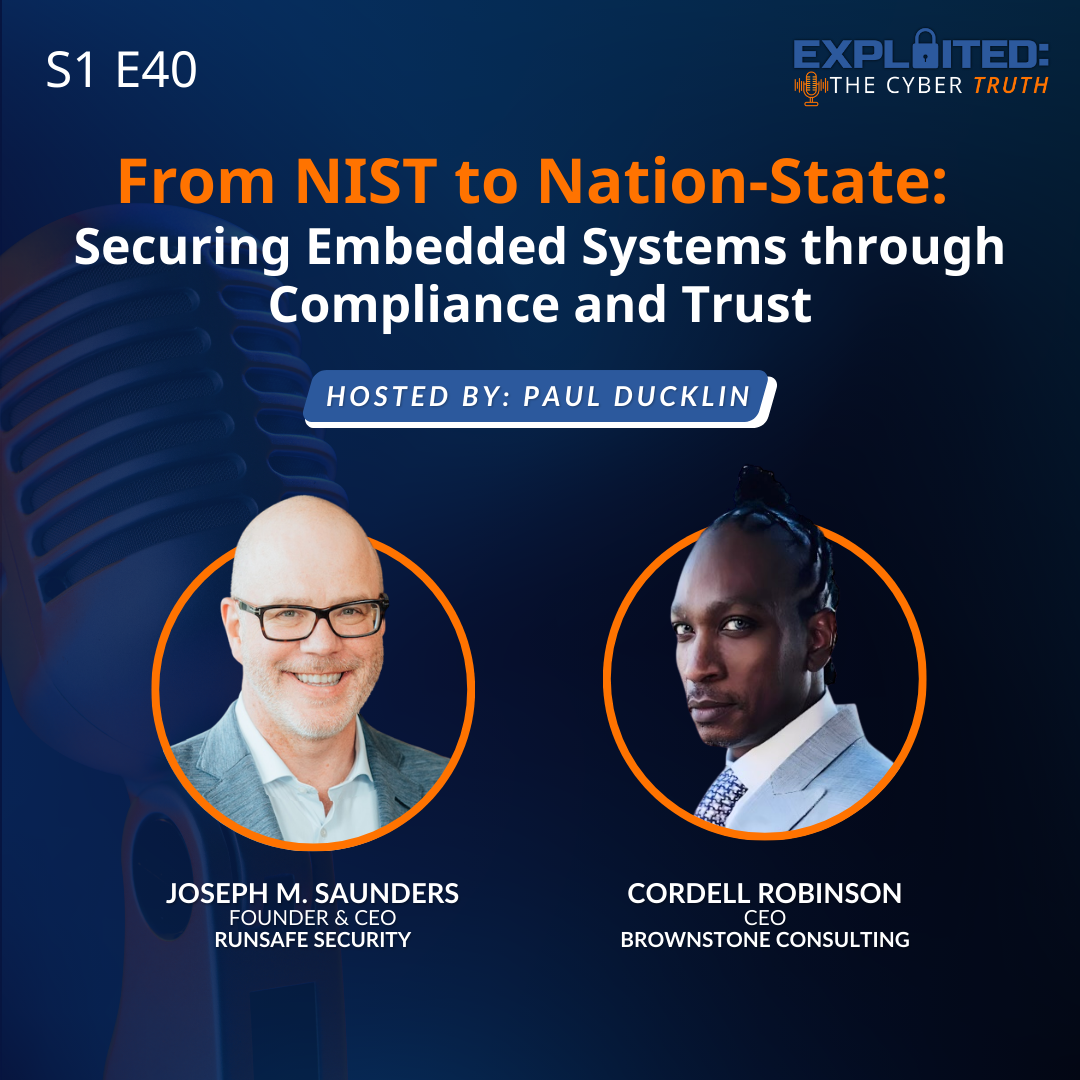
From NIST to Nation-State: Securing Embedded Systems through Compliance and Trust
In this episode of Exploited: The Cyber Truth, Paul Ducklin sits down with RunSafe Security Founder and CEO Joseph...
Get In Touch With RunSafe
Get in touch with RunSafe to learn how our automated cybersecurity solutions can protect your embedded systems, reduce vulnerabilities, and ensure robust, continuous security for your mission-critical software.