Advanced Runtime Protection for Robust Security
RunSafe Security ensures robust runtime protection by integrating security measures directly at build time. This proactive approach incorporates critical defenses into your software from the very beginning, safeguarding your systems during runtime without compromising performance or requiring post-deployment modifications.

Comprehensive Security from Build Time to Runtime
Integrating protection directly at build time, ensures that critical defenses are activated at load time for comprehensive runtime security.
This approach dynamically relocates software functions in memory every time the software is loaded, making it extremely difficult for attackers to find weaknesses to exploit.
Incorporating these protections early in the development process provides robust, continuous security that neutralizes exploit techniques like Return-Oriented Programming (ROP) and buffer overflows, safeguarding your software from potential threats.
“From our perspective, adding RunSafe means we have more opportunity to shrink the attack surface and reduce overall risks for our customers since security is now already built into our product.”
Proactive Threat Mitigation
Ensure software is shielded against threats from the outset, reducing the risk of successful attacks during runtime.
Enhances Software Integrity
Cyber protections embedded at the build stage help maintain the integrity of the software throughout its lifecycle and is more resilient to exploits.
Eliminates Costly Patches
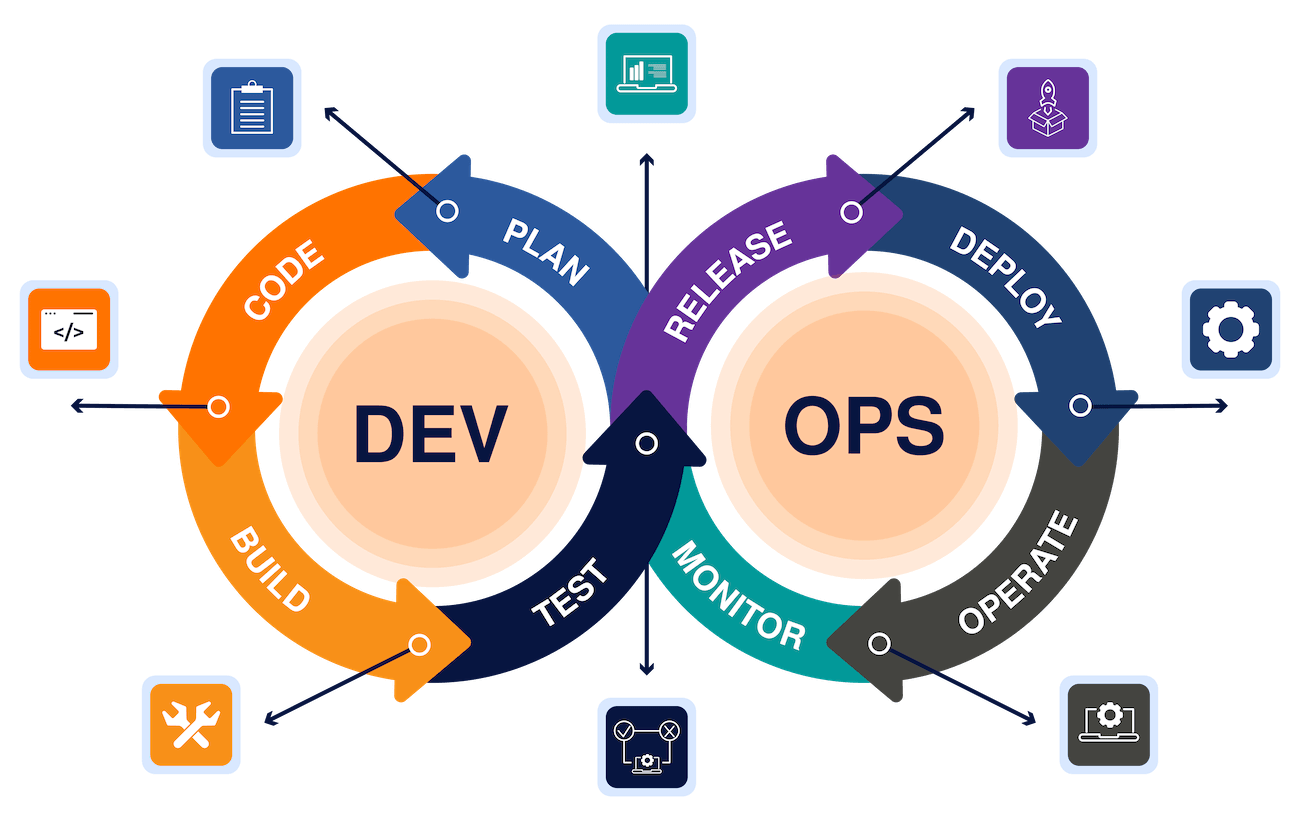
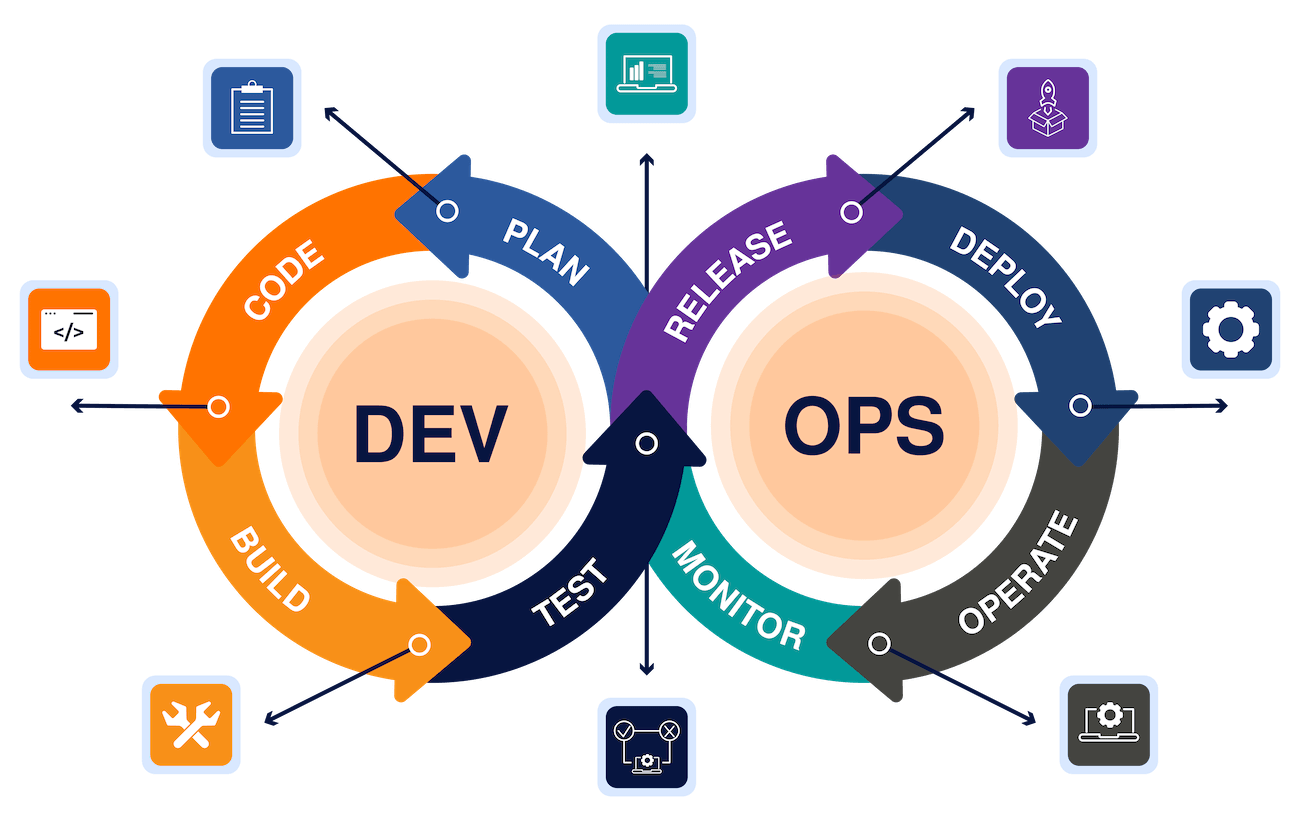
Securing Software from Development to Deployment
The RunSafe Security Platform integrates security early in the development lifecycle to prevent vulnerabilities from being exploited after deployment.
RunSafe’s approach involves embedding security measures directly at build time, which then activate during runtime through advanced techniques like function randomization. By addressing potential threats from the outset, our platform ensures that your software is fortified against a wide range of attack vectors. This proactive strategy not only enhances overall security but also reduces the need for reactive fixes post-deployment.
This process ensures that your software is continuously protected against memory-based exploits.

Enhancing Incident Reponse with RunSafe’s Runtime Protection
Latest Resources
How to Validate SBOM Accuracy for Embedded C/C++ Projects
If you've ever run an SBOM tool on a C/C++ codebase and gotten results that felt wrong, you're not imagining it. Teams evaluating tools like Black Duck, Syft, Trivy, and FOSSA on embedded projects routinely find that outputs are incomplete, inconsistent, or so noisy...
Questions to Ask When Evaluating SBOM Tools for Embedded C/C++
If you're running a proof of concept on Software Bill of Materials (SBOM) tooling for C/C++, you've probably already discovered that vendor demos don't tell you much. Tools that look capable in a sales presentation frequently fall apart when pointed at a real embedded...
The FDA Is Asking for VEX with SBOMs: Here’s Why That Matters
Key Takeaways: The FDA is asking medical device manufacturers to submit VEX (Vulnerability Exploitability eXchange) files alongside SBOMs in some premarket cybersecurity submissions. VEX artifacts document whether known vulnerabilities in SBOM-listed components are...
Ready to Get Started?
RunSafe provides runtime protection by randomizing memory function locations every time software loads, preventing attackers from exploiting vulnerabilities during execution and safeguarding system integrity.


