DevOpsWorld
Win a Lego Millennium Falcon!

Fill out the entry form below and tell us in the message box how securing your CI/CD pipeline could help your organization, we’ll give you a second entry here too!
60-Day Free Trial of RunSafe Security’s Alkemist. Just ask us how!
DevOps, DevSecOps, and RunSafe
Security is one of the most difficult and expensive aspects to automate in DevSecOps, yet DevOps teams are being mandated to take security out of its silo and incorporate it into the software development lifecycle.
Developers, DevOps, and cybersecurity teams are now tasked to:
- Developers, DevOps, and cybersecurity teams are now tasked to:’Shift left” to proactive security rather than reactive remediation for data breach or malware attack scenarios
- Embed code security throughout their entire continuous integration continuous delivery (CI/CD) pipelines; and
- Accelerate delivery and compliance at scale.
Alkemist gives teams the tools to deliver immediately on all three mandates. By injecting memory protection into every software release prior to deployment, Alkemist actively prevents the exploits being used in 70% of cyber kill chains today. Memory protection cannot increase code quality, but it does dramatically decrease the cost and risk of code errors and error prevention and detection methods.
Programs immunized with Alkemist act as a “cyber tourniquet,” preventing critical damage so that dev/DevOps teams can maintain their normal patching schedules, rather than react to emergency interrupts.
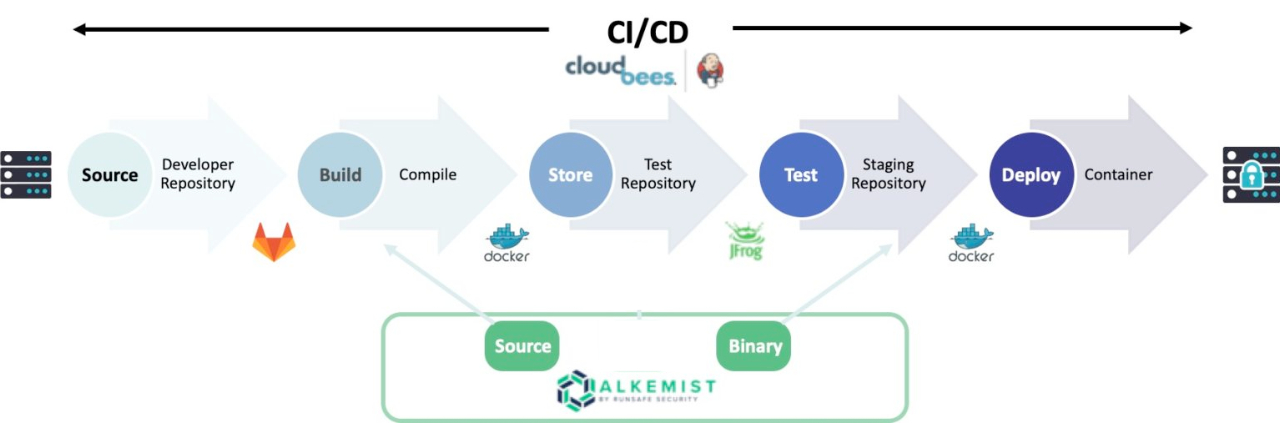
Alkemist also reduces dependence on open source component security and patching timelines, enabling development teams to “fix” related security issues before they happen by making vulnerability exploits impossible. Automating DevSecOps with Alkemist also helps organizations and government agencies deliver applications more rapidly using CI/CD methods, while also automatically incorporating better security with demonstrable controls compliance built into the process.
In addition, Alkemist enables binary security that can be applied easily in cloud implementations, as well as to container orchestration tools such as Kubernetes and Docker Swarm.